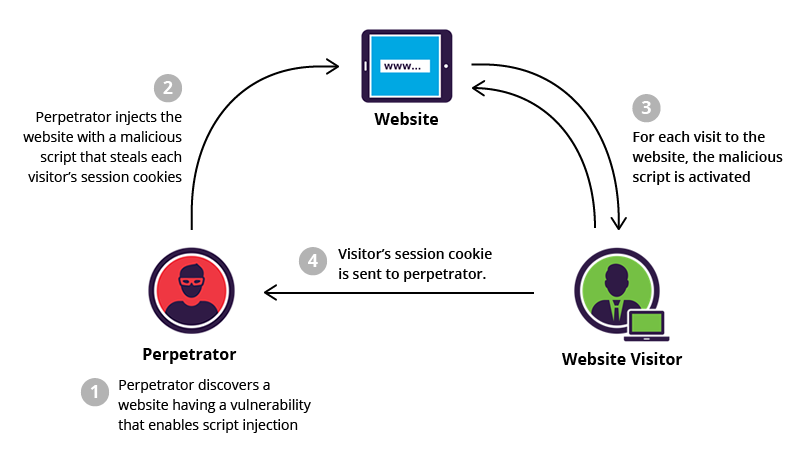
Microsoft has announced a significant enhancement to its Entra ID authentication pipeline designed to protect users from a growing class of external script injection attacks. This update focuses on modernizing and enforcing strict browser security controls during the sign in process, particularly the Content Security Policy that governs what scripts can and cannot run during authentication.
This shift represents one of the most important refinements to Microsoft’s identity protection strategy in recent years. As organizations continue transitioning workloads to the cloud, identity has become the first and most critical security boundary. Threat actors have increasingly targeted this layer with sophisticated code injection techniques that bypass user awareness and compromise credentials at the source. Microsoft’s move directly interrupts this attack surface.
The New Content Security Policy: What Is Changing
Microsoft is deploying a stricter Content Security Policy for all sign ins that occur through the login interface of Entra ID. The policy will enforce the following core controls:
Only Microsoft trusted script sources will be allowed.
Any script not originating from approved Microsoft content delivery network endpoints will be automatically blocked by the browser.
Inline JavaScript will be heavily restricted.
Inline execution will only be permitted for Microsoft authored logic required for secure authentication.
Unauthorized modifications to the sign in page will no longer function.
Browser extensions and third party tools that rely on injecting scripts, adding UI elements, or rerouting logic during authentication will be prevented from executing.
Violating scripts will generate browser console errors.
This allows enterprises to detect interference early while validating internal workflows.
This policy is a direct response to real world attack patterns where malicious scripts attempt to hook into the login process to harvest credentials. With this update, Microsoft is removing that opportunity entirely.
The changes apply exclusively to sign ins that occur through the standard browser based login experience located at login dot microsoftonline dot com. This includes:
Browser based Microsoft 365 authentication
Enterprise Entra ID sign in
Azure portal access
Web based authentications using Microsoft as the identity provider
Other identity experiences, such as Microsoft Entra External ID, are not impacted.
Applications using integrated authentication or device-based sign in flows will continue to function normally.
Impact on Enterprises and Developers
Enterprises must carefully review the tools and browser extensions their workforce relies on. Many organizations use productivity or enhancement extensions that silently inject scripts into web pages including login portals. With the new policy, any extension that modifies the authentication experience will stop functioning.
Examples include:
Password manager extensions that inject fill logic
Browser add ons that modify form fields
Custom monitoring or assistive extensions
User installed productivity extensions that inject JavaScript
Organizations should begin validating their environment by opening browser developer tools, reproducing sign in flows, and checking for Content Security Policy violations. Errors will appear in red, indicating extension interference.
The most important action organizations must take is identifying tools relying on injection based customization and replacing them with officially supported solutions that do not modify authentication pages.
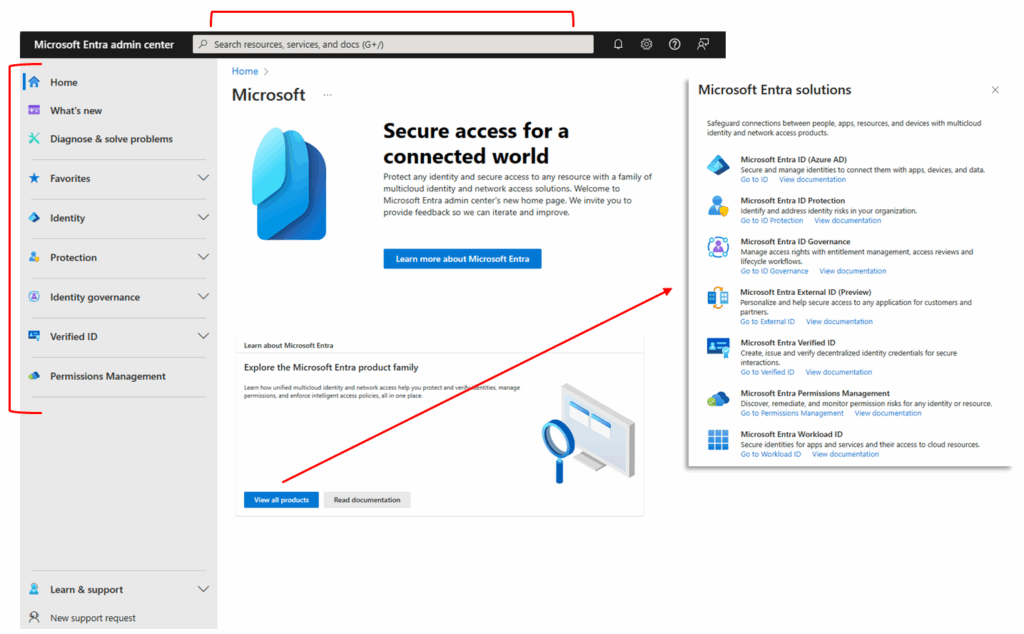
Strategic Importance in Microsoft’s Secure Future Initiative
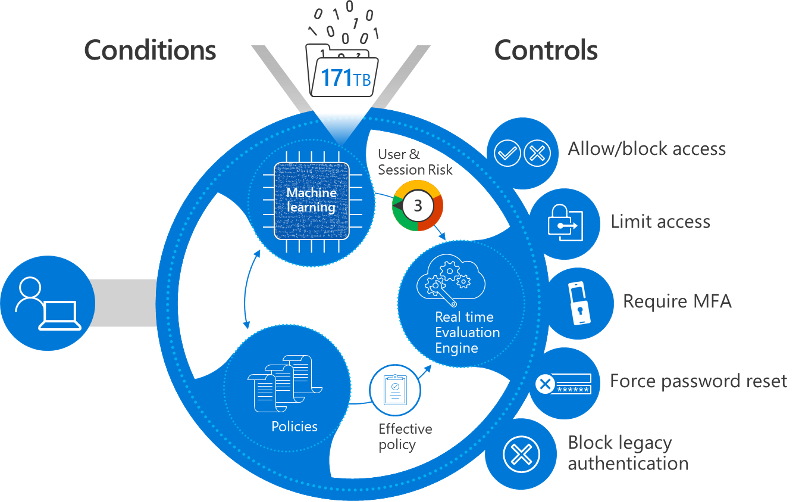

This enforcement is part of Microsoft’s larger Secure Future Initiative, which aims to modernize the foundational security layers of all Microsoft platforms. Identity security is at the center of this effort.
By hardening the browser sign in workflow, Microsoft is reinforcing its zero trust model:
Never trust scripts outside the defined boundary
Minimize the attack surface during authentication
Eliminate high risk legacy behaviors such as unrestricted inline scripting
Ensure identity protection begins before the user even enters their credentials
This creates an authentication ecosystem that is significantly harder for attackers to interfere with. It also ensures that browser based login becomes as protected as device based authentication.
Recommendations for Security Teams Today
Security administrators should begin preparing immediately by conducting a thorough assessment of the organization’s authentication environment.
Recommended preparation steps include:
Review browser extensions used across the enterprise and remove those that modify authentication pages
Test sign in workflows on all major browsers including Chrome Edge and Firefox
Monitor browser console output for CSP violation warnings
Educate users on the upcoming change and prepare support channels for questions
Ensure MFA and conditional access controls are fully deployed as complementary protections
Evaluate internally developed tools to ensure they comply with the new requirements
Update documentation for identity teams service desk staff and IT support
This change will ultimately lead to a more resilient authentication surface, but preparation will ensure organizations avoid disruptions.
Final Summary
Microsoft is taking a firm and proactive step toward securing Entra ID sign ins by eliminating the possibility of external script injection during authentication. By enforcing a strict Content Security Policy, Microsoft is protecting organizations against some of the most common and most effective credential theft tactics used today.
This update significantly strengthens identity security and supports a safer authentication ecosystem for enterprises, cloud administrators, and everyday users.
Sign up For Newsletter!!









Leave a Reply