
A large scale investigation into public GitLab Cloud repositories has uncovered a significant and alarming security problem. A security researcher scanned millions of publicly accessible repositories and discovered more than seventeen thousand exposed secrets. These secrets included active API keys, access tokens, private keys and passwords that could grant unauthorized access to cloud platforms, business applications, development environments and even internal company systems.
This discovery highlights a persistent and dangerous issue in today’s development ecosystem. Public source code repositories continue to leak sensitive information at scale, and attackers are increasingly automating the harvesting of these secrets. For organizations relying on GitLab Cloud, this finding demonstrates that a single overlooked commit can unintentionally expose critical infrastructure.
How the Secrets Were Discovered


The researcher carried out the investigation by using GitLab’s public application programming interface to enumerate every public repository hosted on the platform. More than five million repositories were identified and fed into a scanning pipeline built on a cloud based serverless infrastructure.
A queueing system was used to process each repository efficiently. Each repository name was pushed into a cloud queue, and a serverless function retrieved these entries and scanned them using an automated secret detection tool. The tool inspected files for sensitive data patterns such as credential structures, private key markers, authentication tokens and configuration keys used by common cloud providers.
The entire operation ran for roughly one day and produced a large dataset of exposed secrets. More than seventeen thousand of the detected secrets were confirmed to be live and active, meaning they could be used immediately to authenticate into services or environments belonging to the owners of the repositories.
What the Research Revealed


The findings were more severe than expected. The density of exposed secrets within GitLab repositories was significantly higher than similar audits conducted on other code hosting platforms. The secrets were spread across thousands of projects, ranging from personal repositories to enterprise codebases.
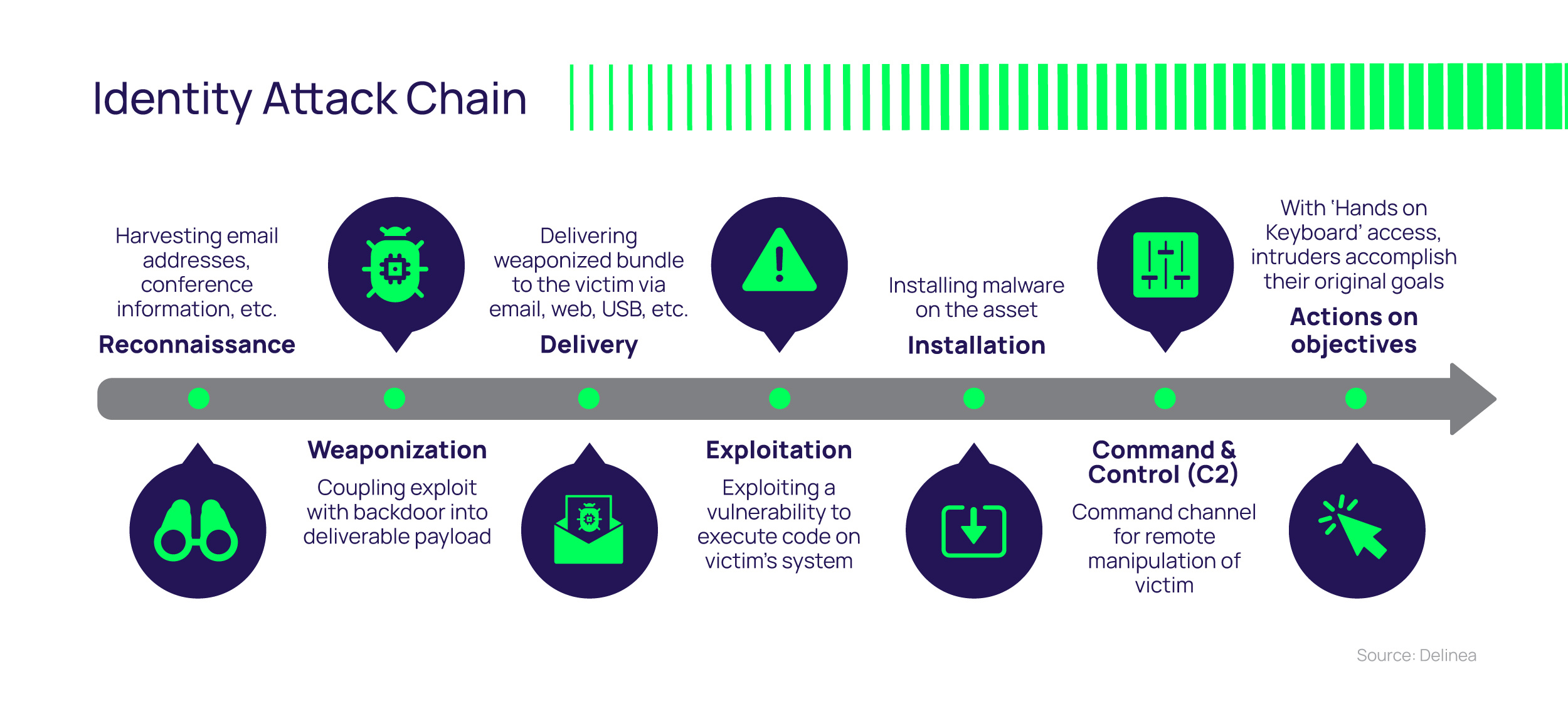
Many of the exposed credentials were directly tied to cloud infrastructure. These included cloud provider access keys, continuous integration tokens, storage access credentials, identity tokens and keys associated with third party services. Because these were active secrets, an attacker could have used them to access sensitive data, deploy malicious code, manipulate development pipelines or pivot deeper into an organization’s environment.
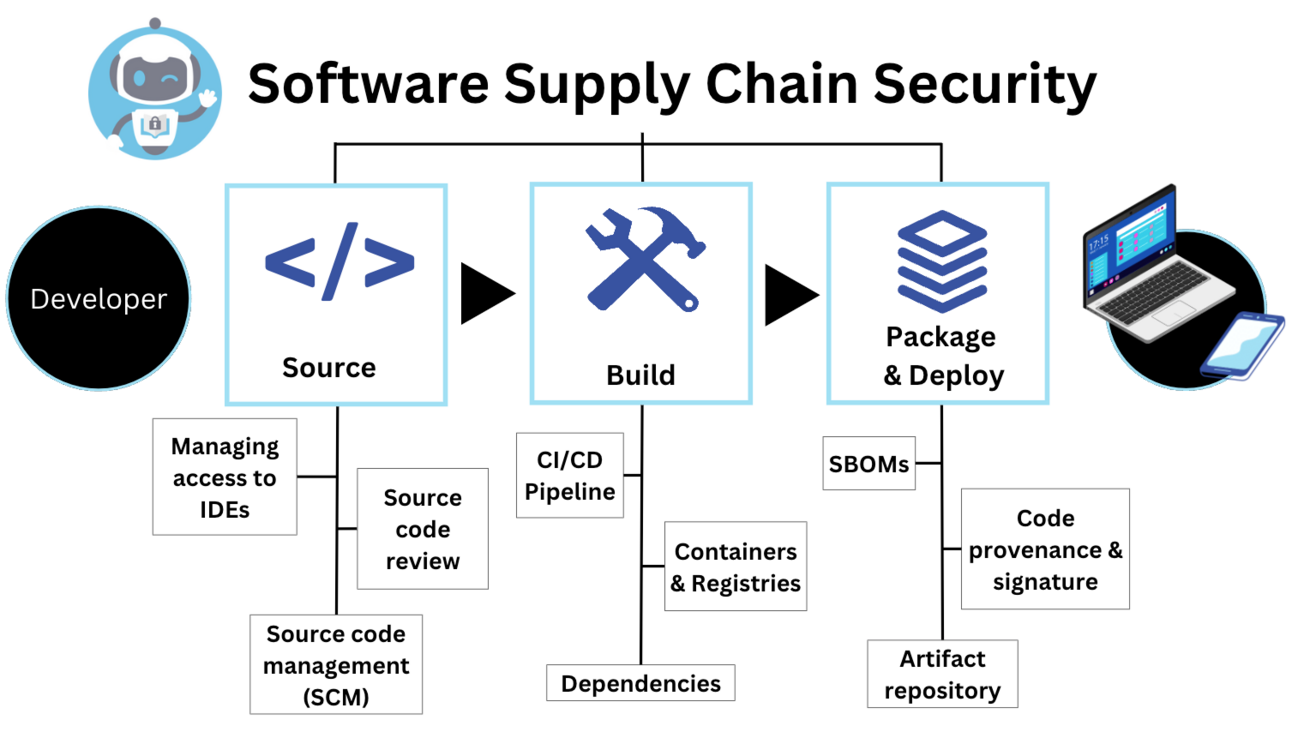
This level of exposure also raises concern for supply chain security. Public repositories containing leaked credentials can be used to compromise software development pipelines, manipulate builds or introduce backdoors into libraries and dependencies distributed to other organizations.
Why This Matters for Development and Security Teams

The discovery emphasizes that secrets management remains one of the weakest points in modern software development. Hardcoded credentials often end up inside repositories due to convenience, misconfiguration or developer oversight. Once committed, even for a moment, they become part of the version history and can be accessed publicly forever unless fully removed and rotated.
For security teams this means the attack surface is significantly larger than most organizations assume. Public repositories must be treated with the same caution as internet exposed services. No secret should ever be committed to source control. This includes personal projects, shared experiments and legacy repositories that developers may have forgotten about.
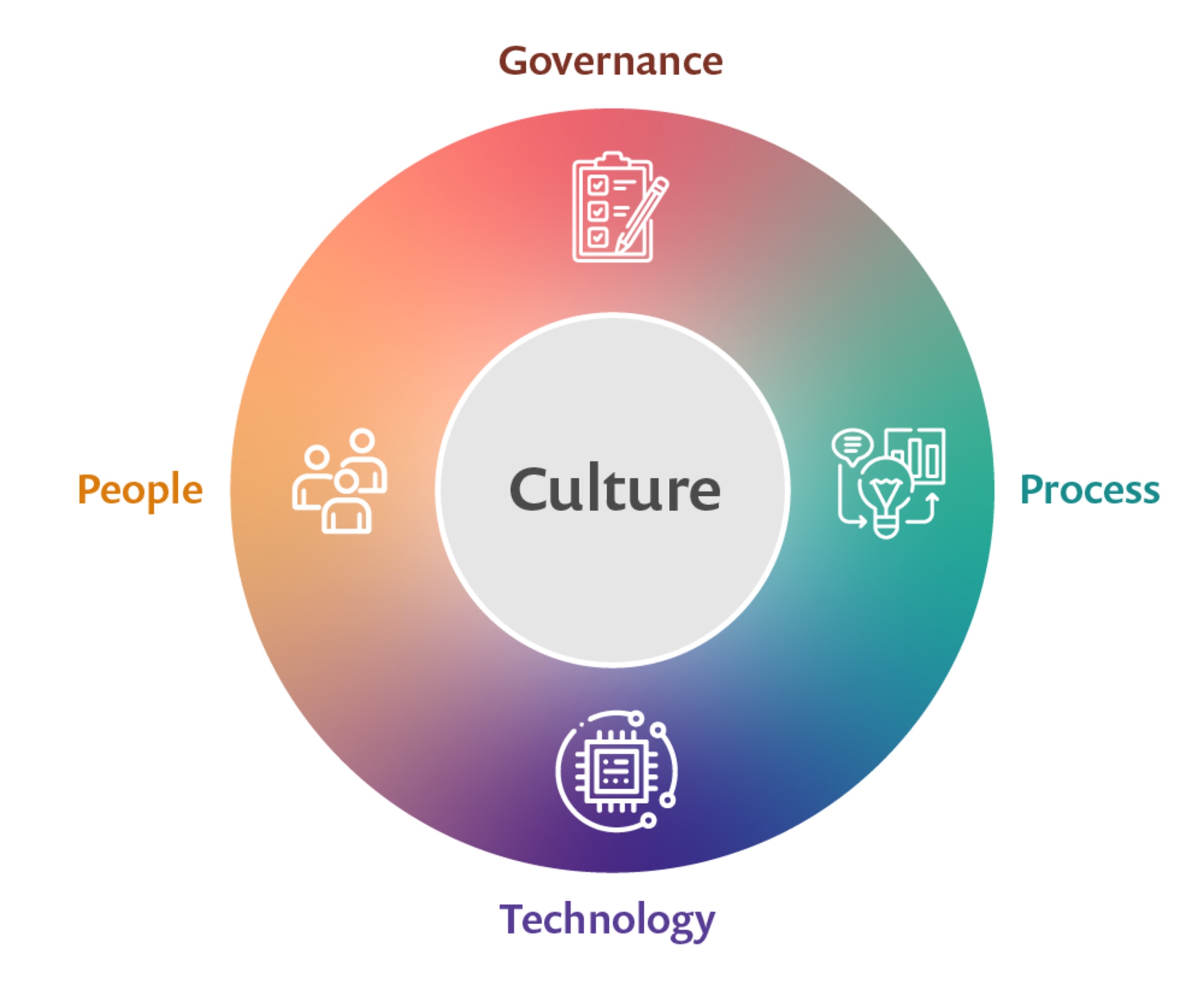
Organizations must adopt a defense strategy that includes:
• Automated secret scanning in every development and deployment pipeline
• Strict policies preventing the use of hardcoded credentials
• Continuous rotation of keys and tokens
• Centralized secret vaults and environment variable based authentication
• Organization wide training on secure coding hygiene
These measures ensure that even if credentials accidentally appear in code, automated systems catch the exposure before attackers do.
The Larger Impact on Cloud and Infrastructure Security

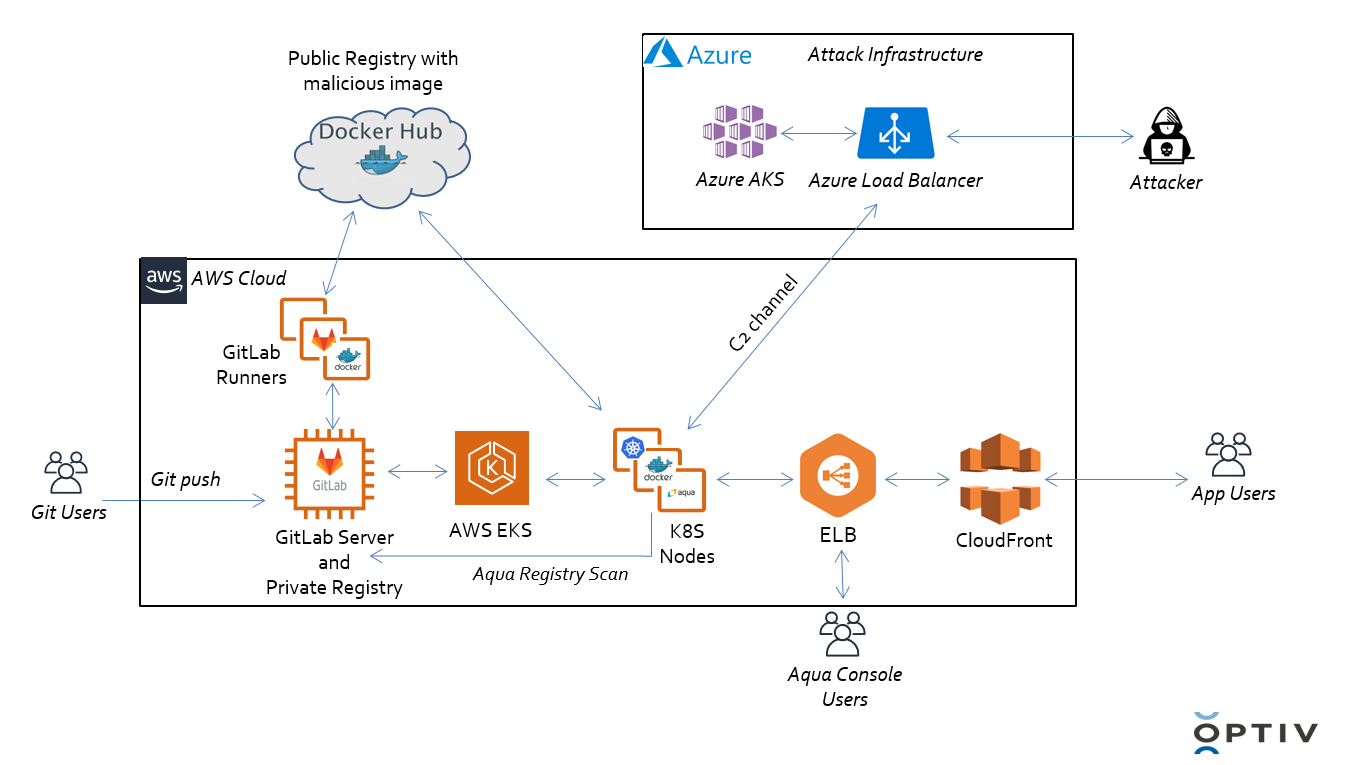

The exposure of thousands of active credentials across GitLab shows how easily attackers can gain unauthorized access to cloud environments. A single leaked access key can be used to read or modify sensitive data, manipulate cloud configurations, or deploy malicious workloads.
In cloud native architectures where services constantly communicate with each other using keys and tokens, the value of these secrets cannot be overstated. If an attacker gains access to them, they may bypass traditional perimeter defenses entirely. This makes exposed secrets one of the most powerful weapons in the hands of cybercriminals.
The event also serves as a reminder that organizations must take supply chain security seriously. An attacker who compromises one developer’s repository can potentially compromise every downstream product, integration or dependency connected to it.
Conclusion
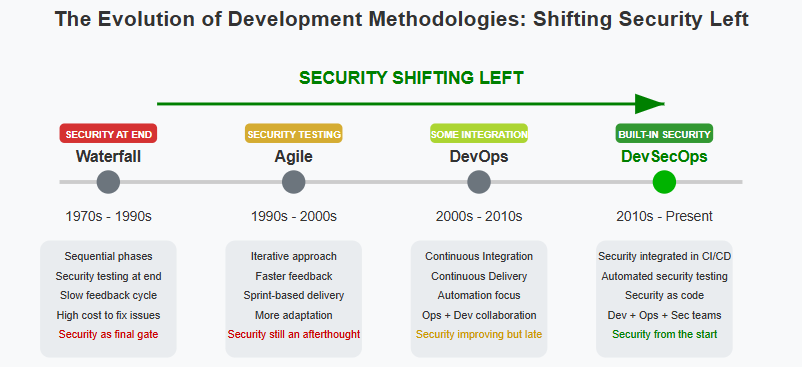
The discovery of more than seventeen thousand active secrets in public GitLab repositories is a clear signal that credential exposure is a widespread and ongoing problem. As cloud adoption grows and development speeds increase, secret leakage becomes more frequent and more dangerous. The only effective defense is to integrate secret hygiene deeply into the culture of development and security.
Automated scanning, secure storage practices, key rotation and continuous auditing are essential. Organizations cannot rely on developers remembering to protect credentials. Security must be built into the workflow at every stage.
Sign up For Newsletter!!









Leave a Reply