A serious insider threat incident has placed the cybersecurity industry on high alert after an employee at CrowdStrike was caught sharing internal system information with known cybercriminals. The incident highlights a growing and often overlooked risk in modern security operations: trusted insiders acting maliciously or being coerced into leaking sensitive information to external threat actors.
Unlike traditional cyberattacks that rely on malware or external intrusions, insider threats stem from legitimate access. This makes detection significantly harder and increases the potential damage when security controls are bypassed from within.
What Happened In the CrowdStrike Incident
CrowdStrike confirmed that an employee was terminated after an internal investigation revealed they had been sharing screenshots of internal systems with a known hacker group. The screenshots reportedly included views of dashboards and internal tools that could help attackers understand security operations and infrastructure layout.
Although CrowdStrike stated that no customer data was breached, the fact that internal operational views were exposed presents a serious security risk. Threat actors can use this intelligence to refine future attacks, evade detection mechanisms, and identify weak points.
The threat group reportedly behind this activity has a history of targeting large organizations using social engineering, insider recruitment, and extortion. This incident shows how even highly mature cybersecurity organizations remain vulnerable to human driven security failures.
Why Insider Threats Are Extremely Dangerous
Insider threats represent one of the most dangerous categories of cyber risk because insiders operate with legitimate credentials, trusted devices, and approved access paths.
This type of threat can bypass perimeter defenses, evade traditional endpoint detection, and blend in with legitimate operational activity. When combined with financial incentives from threat actors, insiders can become an extremely powerful attack vector.
In this case, the risk was not malware but knowledge leakage. Once internal security workflows are exposed, attackers can design more sophisticated campaigns.
Indicators of Compromise and Detection Signals
Security teams should actively monitor for behavioral and operational indicators linked to insider data leakage. Below are relevant indicators of compromise and red flags associated with incidents like this:
Unusual creation or transfer of screenshots from corporate systems
Unauthorized use of screen capture tools or recording utilities
Outbound transfer of image files to external destinations
Internal accounts accessing sensitive dashboards outside normal job functions
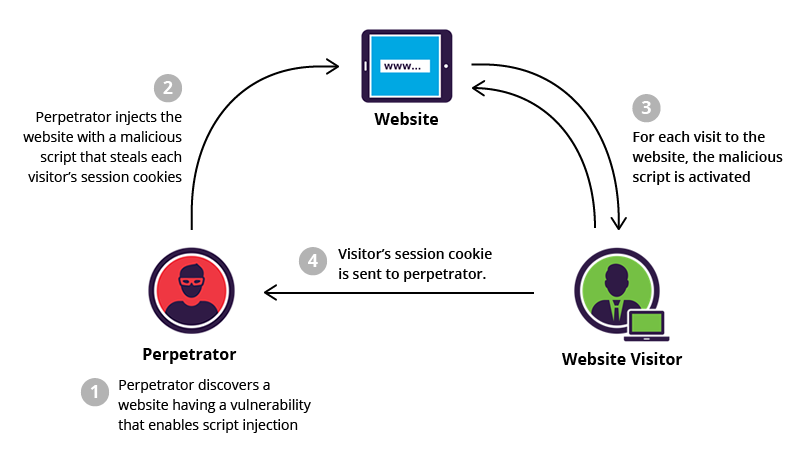
Abnormal session token or single sign on cookie access patterns
Sudden spikes in data uploads from user endpoints
Claims by threat actors referencing internal system screenshots
Employee accounts showing unusual login times or abnormal access frequency
These indicators should be treated as high risk and investigated immediately.
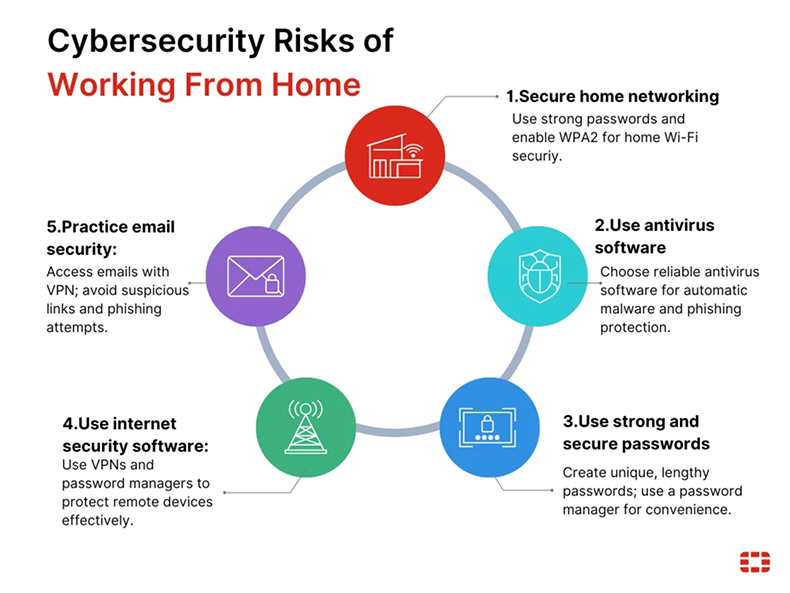
How Organizations Can Protect Against Insider Threats
Organizations must treat insider threats as a core security risk, not a secondary concern.
First, access control should strictly follow the principle of least privilege. Employees should only access systems directly required for their role.
Second, continuous user behavior monitoring should be implemented. Security teams should baseline normal employee activity and flag deviations, especially around data movement and access to sensitive systems.
Third, strong offboarding procedures must be enforced. When an employee is terminated or resigns, access must be revoked instantly, active sessions invalidated, and devices secured.
Fourth, organizations should implement data loss prevention policies that detect and block unauthorized data transfers, including screenshots and file uploads.
Why This Incident Matters to the Cybersecurity Industry
This case sends a strong message to the industry. Even elite security vendors are vulnerable to insider driven threats.
Security leaders must expand their focus beyond malware and perimeter defense to include human risk management. Insider risk must be monitored with the same urgency as external adversaries.
Threat actors increasingly seek insiders because it is often easier and more reliable than exploiting technical vulnerabilities.
Final Thoughts
The CrowdStrike insider incident is a real world example of how trust can be weaponized. When attackers gain influence over internal users, even the strongest technical defenses can be bypassed.
Every organization must strengthen insider threat detection, monitor internal behavior, and implement strict data handling controls. Insider risk is no longer theoretical. It is one of the most effective attack methods being used in real threats today.
Organizations that fail to adapt to this reality will remain exposed to one of the most silent and damaging attack vectors in cybersecurity.
Sign up For Newsletter!!









Leave a Reply