Cox Enterprises has confirmed a data breach involving its Oracle E-Business Suite environment after threat actors exploited a previously unknown vulnerability. The incident highlights the growing risk to enterprise resource planning systems and the serious business impact that can result when core financial and operational platforms are compromised.
This breach has drawn widespread attention because attackers targeted high value back office infrastructure instead of traditional perimeter systems. Oracle E-Business Suite is commonly used to manage payroll, vendor payments, procurement, and internal financial data, making it an extremely attractive target.
What Happened
Cox Enterprises detected suspicious activity within its Oracle E-Business Suite environment after attackers exploited a zero day vulnerability. The intrusion is believed to have occurred over several days before internal security teams identified the breach.
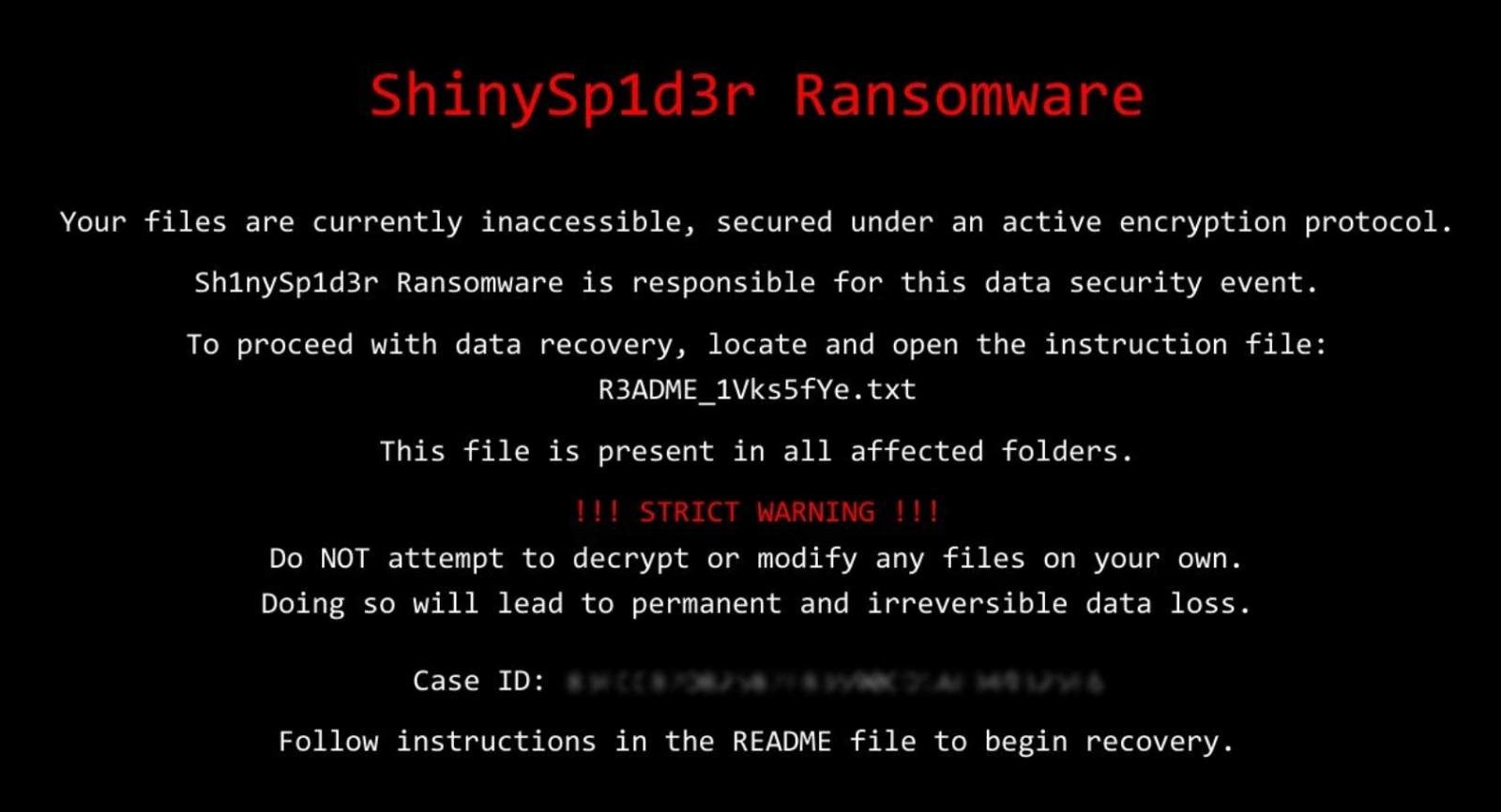
The attackers accessed sensitive internal systems and extracted data. The organization later confirmed that personal information belonging to thousands of individuals was impacted. Threat actors eventually published information about the breach as part of an extortion strategy.
Cox notified affected individuals and began working with security teams to contain the intrusion and assess the full scope of the damage.
Why This Breach Matters
This incident demonstrates a dangerous trend in cyber attacks. Instead of focusing only on endpoints or phishing campaigns, attackers are increasingly targeting enterprise resource planning platforms that contain large volumes of sensitive data.
Oracle E-Business Suite environments often have broad network trust relationships with other internal systems. Once compromised, attackers can pivot into finance, identity, and human resources systems without triggering traditional perimeter alerts.
The breach also shows how effective zero day exploits remain. When vulnerabilities are unknown to software vendors, organizations have no patches or signatures to rely on, leaving detection and behavior monitoring as the only real defenses.
Technical View of the Attack
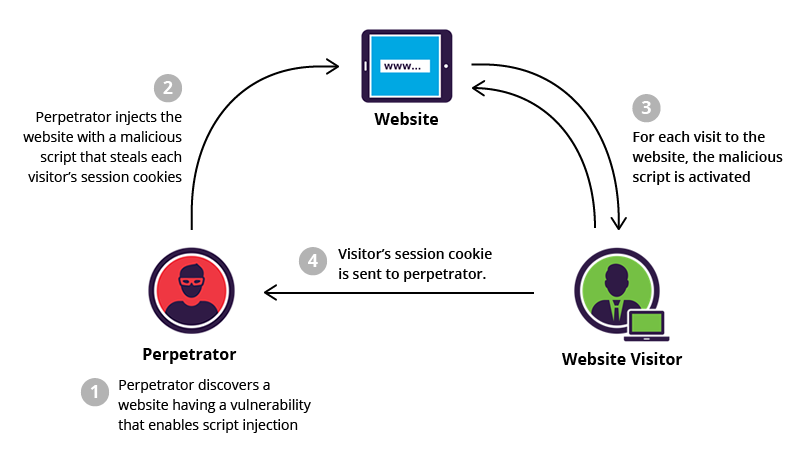
Attackers exploited a vulnerability in Oracle E-Business Suite that allowed unauthorized access to protected application layers. This led to privilege escalation and full access to backend data repositories.
Once inside, the attackers conducted reconnaissance, expanded their privileges, and initiated bulk data extraction. This activity was designed to go undetected and focused on collecting valuable personal and financial information.
Following the theft, attackers used an extortion model by publicly naming the victim organization and threatening further data exposure.
Indicators of Compromise and Suspicious Behavior
Security teams should monitor the following indicators when defending Oracle E-Business Suite environments:
Unusual HTTP or HTTPS requests to Oracle E-Business Suite services
Large volumes of outbound data leaving ERP servers
Unexpected administrative logins or privilege changes
Database queries accessing large tables or exporting records
Outbound connections to unfamiliar IP addresses or domains
Unexpected creation of scheduled tasks or background services
Mentions of internal company names in extortion or leak campaigns
These indicators should trigger immediate investigation and incident response.
Immediate Actions Organizations Should Take
Organizations running Oracle E-Business Suite should treat this type of event as a critical risk and act quickly.
First, inventory all Oracle E-Business Suite systems and identify their exposure to external networks.
Second, apply the latest security updates and hardening configurations.
Third, conduct thorough log reviews covering authentication activity, data movement, and privilege changes.
Fourth, segment enterprise resource planning servers from the rest of the internal network.
Fifth, prepare incident response plans to handle data theft and public extortion scenarios.
Key Lessons for Security Professionals
Enterprise resource planning systems are no longer low profile targets. They are high value assets.
Zero day vulnerabilities will continue to be weaponized quickly by organized cybercriminal groups.
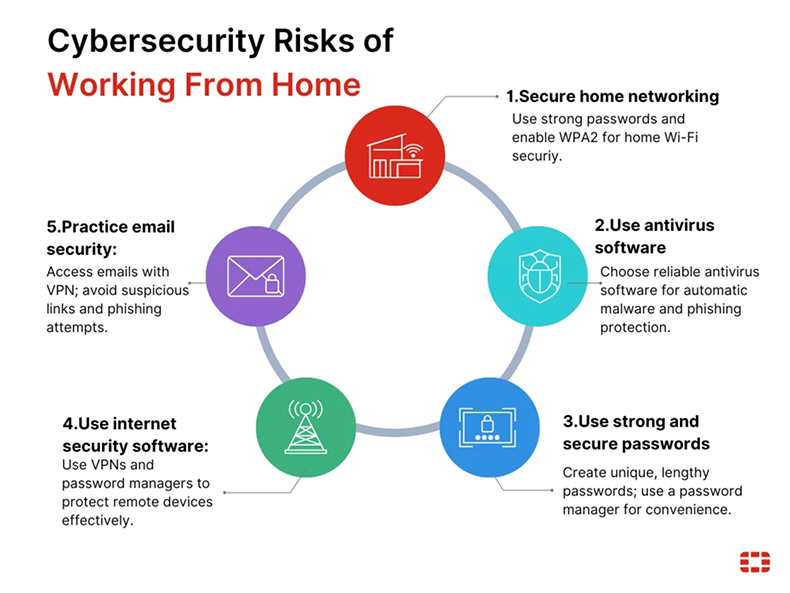
Defensive strategies must evolve beyond patching and include behavioral analytics, anomaly detection, and strict network segmentation.
Organizations that fail to protect ERP environments face significant financial, regulatory, and reputational consequences.
Final Thoughts
The Cox Enterprises breach serves as a powerful reminder that critical business systems are now frontline targets in modern cyber warfare.
Effective defense requires visibility into internal application behavior, strong identity controls, and rapid incident response capabilities.
As attackers become more strategic, organizations must be faster, more observant, and more disciplined in securing their most valuable systems.
Sign up For Newsletter!!










Leave a Reply