The Cybersecurity and Infrastructure Security Agency has issued a high priority alert warning organizations about an actively exploited remote code execution vulnerability in Oracle Identity Manager. This flaw allows attackers to gain full control of vulnerable systems without authentication, making it one of the most dangerous identity security risks currently facing enterprises and government agencies.
This vulnerability affects a core enterprise identity platform used to manage user access, authentication, and system privileges. Because identity infrastructure sits at the center of enterprise security, exploitation of this weakness can lead to domain wide compromise, data theft, and long term persistence by threat actors.
What makes this threat critical is that exploitation is already happening in real world attacks, not just in research environments. Security teams must treat this as an emergency level vulnerability.
Understanding the Oracle Identity Manager Vulnerability
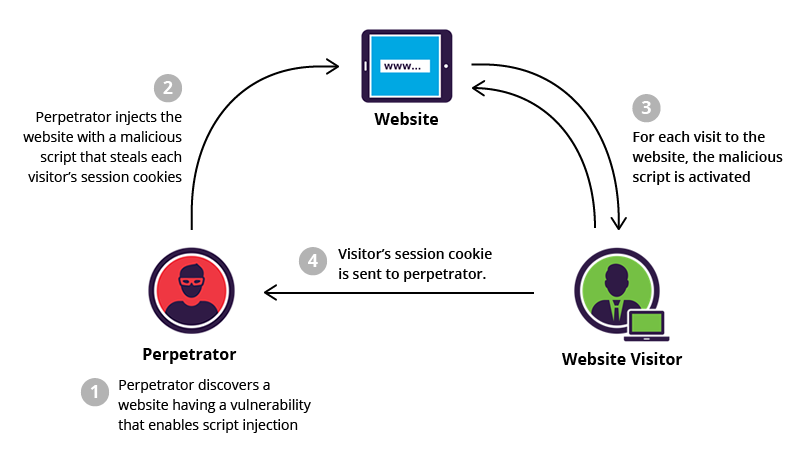
The flaw is classified as a pre authentication remote code execution vulnerability. This means attackers do not need valid login credentials to exploit it. They can directly send specially crafted requests to public facing application programming interface endpoints and gain execution privileges on the underlying server.
The vulnerability stems from a weakness in the way Oracle Identity Manager validates access to protected API routes. By manipulating URL paths with specific parameters, an attacker can bypass authentication controls and access restricted system functionality.
Once inside, the attacker can submit malicious payloads through exposed scripting mechanisms and force the server to compile and run arbitrary operating system commands. This results in full system level access under the permissions of the Oracle service account.
This type of flaw represents one of the most severe classes of security bugs because it removes all traditional access barriers.
Why This Vulnerability Is Extremely Dangerous
This issue is especially high risk for several reasons.
First, it requires no user credentials. Any internet facing Oracle Identity Manager instance can be targeted remotely.
Second, exploitation results in full remote code execution, giving attackers the ability to install malware, create backdoors, harvest credentials, and move laterally through the network.
Third, identity management platforms are high value targets. If an attacker compromises this layer, they can manipulate access controls, create privileged users, and access downstream systems like Active Directory, cloud identity providers, and single sign on services.
Fourth, government agencies and large enterprises heavily rely on Oracle Identity Manager for critical infrastructure, increasing the potential impact of successful attacks.
How the Attacks Are Being Carried Out
Active attacks observed in the wild follow a predictable pattern.
Attackers scan the internet for exposed Oracle Identity Manager servers. Once found, they send crafted HTTP requests to vulnerable endpoints to bypass authentication. After gaining access, they trigger scripting features within the application to execute system commands.
In real attack campaigns, threat actors have been observed probing API routes related to application management and script compilation features. After exploitation, compromised servers often begin making unusual outbound network connections, running unauthorized processes, or communicating with external command and control infrastructure.
These early signals are critical detection points for security teams.
Indicators of Compromise to Watch For
Security operations teams should monitor for the following behavioral patterns:
Unexpected HTTP requests targeting Oracle Identity Manager API endpoints
URL manipulation attempts using uncommon suffixes or serialized requests
Sudden appearance of script compilation or execution events in application logs
Unrecognized administrator accounts appearing in the identity system
Outbound network traffic from identity servers to unknown external IP addresses
New scheduled tasks, services, or background processes running under Oracle service accounts
Any of these findings should be treated as a potential security incident.
Immediate Actions Organizations Should Take
All organizations using Oracle Identity Manager should act immediately.
First, locate all deployed instances of Oracle Identity Manager. This includes on premises servers, cloud deployments, and hybrid identity environments.
Second, determine whether any of these systems are exposed to the internet or accessible from untrusted networks.
Third, apply Oracle’s latest security patches that address the vulnerability. Systems that cannot be patched immediately should be isolated using firewall rules and network segmentation.
Fourth, conduct a full log review and threat hunt covering several months of historical data. Because attackers may have been exploiting this weakness before public disclosure, retrospective analysis is essential.
Fifth, restrict network access to identity infrastructure. Identity servers should never be broadly exposed and should be isolated behind strong access controls.
Long Term Defensive Strategy
This incident highlights a critical lesson for modern enterprise security.
Identity systems are no longer just support infrastructure. They are high value attack surfaces that require the same level of monitoring, segmentation, and hardening as domain controllers and critical application servers.
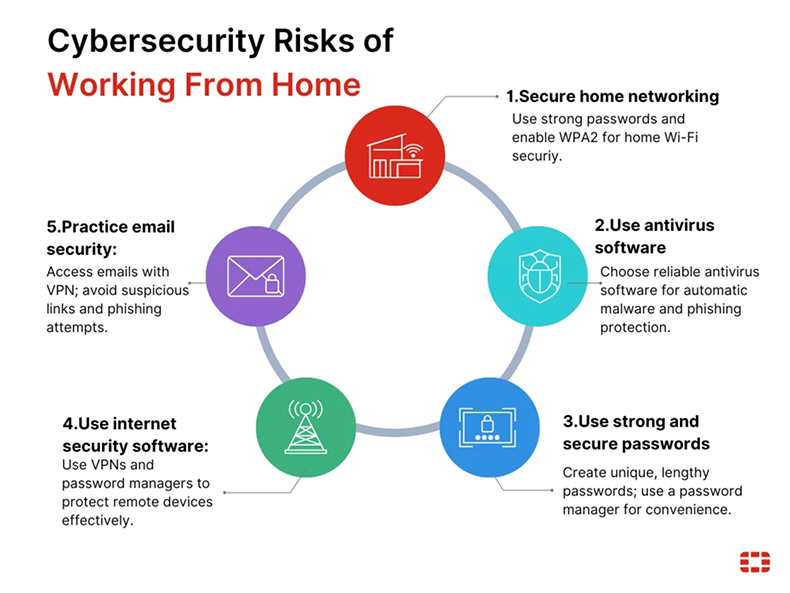
Organizations should adopt a zero trust architecture for identity services, enforce least privilege policies, and continuously monitor for abnormal identity system activity.
Security teams should also prioritize pre authentication remote code execution vulnerabilities in their patch management workflows, as these flaws allow the fastest and most damaging compromises.
Final Thoughts
The active exploitation of this Oracle Identity Manager vulnerability represents a serious global threat. Attackers are specifically targeting identity infrastructure because of the access and control it provides.
Organizations that delay patching or fail to monitor their identity systems are at extreme risk. Immediate remediation, deep log analysis, and strong architectural controls are no longer optional.
Strengthening identity security today is one of the most effective ways to prevent catastrophic breaches tomorrow.
Sign up For Newsletter!!









Leave a Reply